A user name and a password are not enough. An increasing number of Internet services are opting for multifactor authentication as being more secure. In this area, eGovernment with its high security standards can serve as a role model. Taking as an example the authentication service authega, we present a tried and tested certificate-based process. We also discuss current trends in biometrics and one-time, single-use passwords.
Authentication services are the bouncers of the online world.
Authentication services are the bouncers of the online world. They largely decide who gains access to access-restricted websites and who doesn’t. In the past, users tended mostly to be waved through rather negligently. A user ID and a valid password were all that you needed, but calls for more secure and more flexible access procedures are growing louder. For one, more and more areas of life with sensitive data are transferred to the Internet. For another, well-publicized data breaches in recent years[1] – from Sony’s Playstation network via Yahoo to Ashley Madison and involving user data by the million – have led to a greater degree of security awareness.
Unlike most industries, where application security was neglected for years, the eGovernment sector has always set great store by high security standards. That is why other industries are well advised to take a closer look at the methods eGovernment uses. Before dealing with established authentication methods we will first outline the basics of registering with an online service.
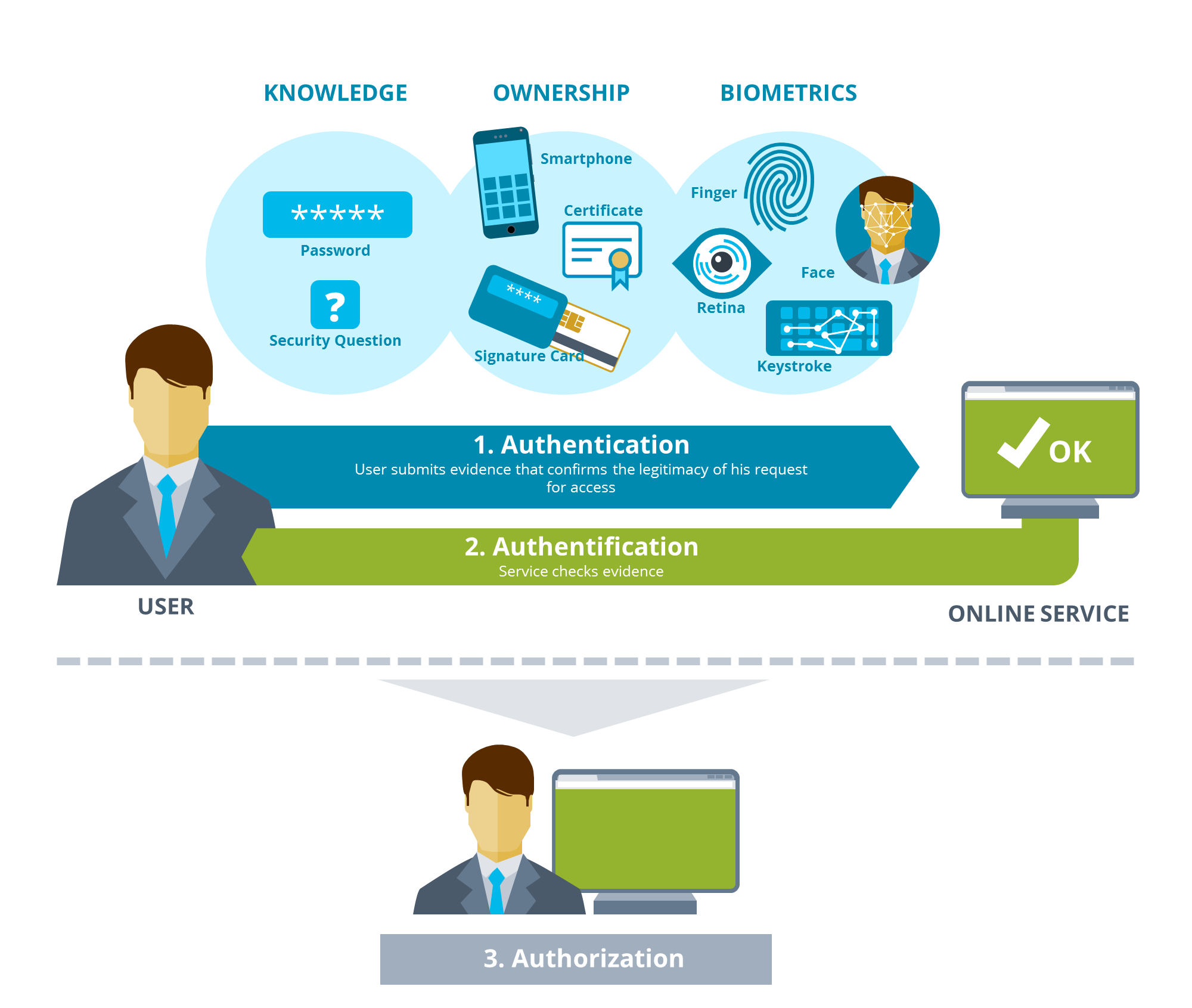
For authentication, users provide evidence to confirm the legitimacy of their access request. Users authenticate themselves by means of something they:
- Know, such as a password,
- Possess (a token, such as a USB stick, or a certificate)
- Or have as personal characteristics, such as a fingerprint, a retina scan, a voiceprint, or keystroke biometrics.
During authentification this evidence is checked by the service. When several pieces of evidence are involved this may also be referred to as multifactor authentification. Successful authentification leads to authorization. That defines which roles and rights users are assigned and which functions they are allowed to use. What now follows deals solely with authentication and authentification.
Certificate-based Authentication – A Tried and Tested Solution
A procedure that is widely used in eGovernment, including Germany’s ELSTER electronic tax return system and the authega authentication component, uses certificates and is based on a public key infrastructure (PKI). Everyone in Germany who has filed a tax return electronically will be familiar with the process. After registration the user receives a certificate that is secured by a number or a password. So authentication is based on something the user has (the certificate) and on something he or she knows about it (the PIN).
What is authega?
authega, short for Authentication for eGovernment Applications, is an authentication service developed jointly by the federal state of Bavaria, mgm, and secunet AG. authega is based on security functions originally developed for the electronic tax return ELSTER. authega has been available as a separate authentication component since 2010 and is now used by a large number of public bodies. A special characteristic of authega is that it is designed solely for authentication and authentification and is deliberately and totally decoupled from authorization functions such as the assignment of rights and roles. That enables the secure authentication component to be used flexibly and makes data protection guidelines easier to implement.
The certificate may provide secure access but it must not get into the wrong hands. That is why authega incorporates an initial registration process that checks the user’s identity before the certificate is issued. The registration data is sent on two channels: by email and via the postal service. This ensures that the access data reaches the right hands. A hacker would need to access the physical mailbox to which the registration code was sent. Services like ELSTER obtain their address data directly from existing sources.
Authentication methods with different security levels are also available. The most widespread in ELSTER’s case are soft certificates – digital certificates with their respective public and private keys that are stored as files on the computer or on an external storage medium. The disadvantage is that they can be lost in the depths of the file system or, in the worst case, be copied and so get into the wrong hands unnoticed. Very few people store the soft certificate on a USB stick and keep the stick with their tax documents – out of reach for hackers.
For a higher level of security there are signature cards that contain the certificate on a chip and cannot be copied. They look like check cards and are issued by trustworthy certification providers such as employers or, in ELSTER’s case, for example, by the Federal Chamber of Notaries, the Bundesdruckerei or the DATEV co-operative. To use signature cards, users need special card readers. They work in much the same way as an ATM. You first insert the card into the reader and then enter your PIN, but instead of withdrawing cash you prove your identity to an online service and can sign documents electronically. In spite of the higher level of security, however, signature cards are seen as exotic among authentication methods because they are so little used, and much the same can be said so far of the new German identity card’s authentication functionality.
Forms that formerly had to be printed, filled out, signed and returned can now be dealt with electronically.
In addition to authentication, systems like authega currently play an important part in setting up electronic processes. The Bavarian e-Government Act (BayEGovG), for example, promotes a far-reaching alternative to the written form as long as a sufficiently secure[2] authentication process, such as authega, is used. Forms that formerly had to be printed, filled out, signed and returned can now be dealt with electronically. The certificate serves as an electronic signature. Registration by certificate is seen as giving the web session a midrange confidence level, and making the declaration of intent and mailing the form’s contents are considered to meet or replace the written form requirement. The certificate is also used to sign and encrypt content that is sent to members of the public.
The Problem of Data Protection
Another subject area that has been discussed for years in connection with eGovernment applications is data protection. Public sector standards are, as a rule, higher than in other industries. Many companies have ground to make good in this area, especially in view of Europes General Data Protection Regulation, which includes inter alia the “right to be forgotten.” Here too, authentication plays a key role as the first point of contact between users and online services.
In authega the data protection problem is addressed by limiting its functionality to authentication. The system consists for one of a central component where certificate management in its entirety takes place, including the generation of new certificates and login checks. For another the system provides a local component for each client. It is located before the client’s subject proceedings and serves as the interface to the central system.
This strict separation of downstream identity management systems makes authentication possible without holding personal data.
Pseudonymous IDs are used for authentication – different ones for each client. All that authega reports to the subject proceedings is that “a user with this pseudonymous ID has logged in successfully.” This strict separation of downstream identity management systems makes authentication possible without holding personal data. That prevents a citizen’s identity from being revealed across several cases (clients) without the individual’s consent even though a central authentication system is in place.
Context-sensitive Security Level and One-Time Passwords
A current trend in authentication is to upgrade or downgrade the security level depending on the context. If, say, a user regularly logs in from Berlin with the same browser on his desktop a user name and password will suffice. If, in contrast, a login attempt is made for this user from a mobile device in Dublin an additional authentication factor such as a confirmation code sent to the smartphone will be required. Google already uses context-sensitive two-factor authentication of this kind.
In recent years the OTP, or one-time password, has come into widespread use. Its unique feature is that each password is used once only, thereby frustrating replay attacks using previously recorded data. TANs, or transaction numbers, in online banking are a classic example of an OTP process.
Today, OTP generators are increasingly used instead of TAN lists. RSA Security’s SecurID, for example, uses a hardware token in the form of a key ring. The token generates a new number every minute and shows it on a small display. With the growing use of mobile devices hardware tokens of this kind are increasingly being superseded by apps. A widespread example is the Google Authenticator app, which in addition to a Google account protects services such as Facebook, Dropbox and Outlook by generating one-time passwords. Even the computer games manufacturer Blizzard offers its customers an app to provide better protection for their accounts by means of OTPs.

One-time or single-use passwords could become a groundbreaking procedure for eGovernment. Their security level is comparable to that of certificates and their ease of use is significantly greater. Users do, after all, always have a mobile device on them. The process has been tried and tested for several years, and except for some patented OTP technologies it has been very largely disclosed, such as in RFC 1760 (S/KEY), RFC 2289 (OTP), RFC 4226 (HOTP), and RFC 6238 (TOTP).
Retina Scan, Voiceprinting, Keystroke Biometrics
An entire range of biometric processes is now also available, although some of them involve significant data protection risks[3]. The classics include retina scans and fingerprinting. Newer options are voiceprinting – identifying somebody by means of their voice – and keystroke analysis – how they use a keyboard.
The biometrics boom is closely linked to the mobile revolution. Smartphones all come with sensors, cameras and microphones, and some even incorporate a fingerprint reader. So a wider range of users is now aware of biometric methods. Yet in spite of the steady growth of biometric processes their security level is limited. In contrast to a password, which has to be an exact match, biometric methods are based on probabilities, defining threshold values beyond which a voice, for example, is accepted as being that of the authorized person. Whenever a new biometric method is presented the first hacks do not, as a rule, take long to put in an appearance.[4]
Conclusion
Much is on the move in authentication at present. Google, Apple, Amazon, Facebook, PayPal, Instagram, and many others now regard it as such a sensitive issue that they offer their users two-factor authentication. In the online world biometric methods have so far tended to be more of an area for experimentation – and to be somewhat insecure for mass market use.
Experience gained in the public sector has shown that certificate-based authentication, implemented correctly, is a sufficiently manageable way to safeguard services with millions of users in a large number of use cases. Authentication by means of certificates does, however, have weaknesses. It is a costly and time-consuming process. Users often mislay or lose their soft tokens and their passwords can be cracked offline by means of brute force attacks. That is why the eGovernment sector is constantly on the lookout for alternative methods. Modern OTP methods with single-use passwords generated ad hoc are an alternative to be taken seriously and could soon make a major breakthrough as an addition to existing certificate-based PKI processes.
[1] For a good overview see the infographic World’s Biggest Data Breaches.
[2] Cf., for example, §2 BayBITV, Art. 9 of the Bavarian eGovernment Act (BayEGovG) of Dec. 22, 2015
[3] For an initial overview see the Arbeitspapier zu Biometrie in der Online-Authentifizierung of the international Working Group on Data Protection in Telecommunications.
[4] See, for example, the Chaos Computer Club’s hacks of the Samsung S8 Iris-Scan and the Apple Touch ID.
Image Source: Fotolia / Jörn Buchheim